Blog
Dive deep into MikroTik's RouterBoards and RouterOS. We keep you informed and up-to-date, always.
Blog
Dive deep into MikroTik's RouterBoards and RouterOS. We keep you informed and up-to-date, always.
Author
Every post is penned by our certified MikroTik engineers, ensuring relevance and accuracy in every word.

Feedback
Your insights drive our content. Sharing knowledge, we elevate the MikroTik community in Canada together.
Easier than You Think!
DoS and DDoS attacks are two of the most prevalent types of malicious cyber activities that threat devices, servers and networks, victimizing Internet users regardless of size, location, industry, etc.
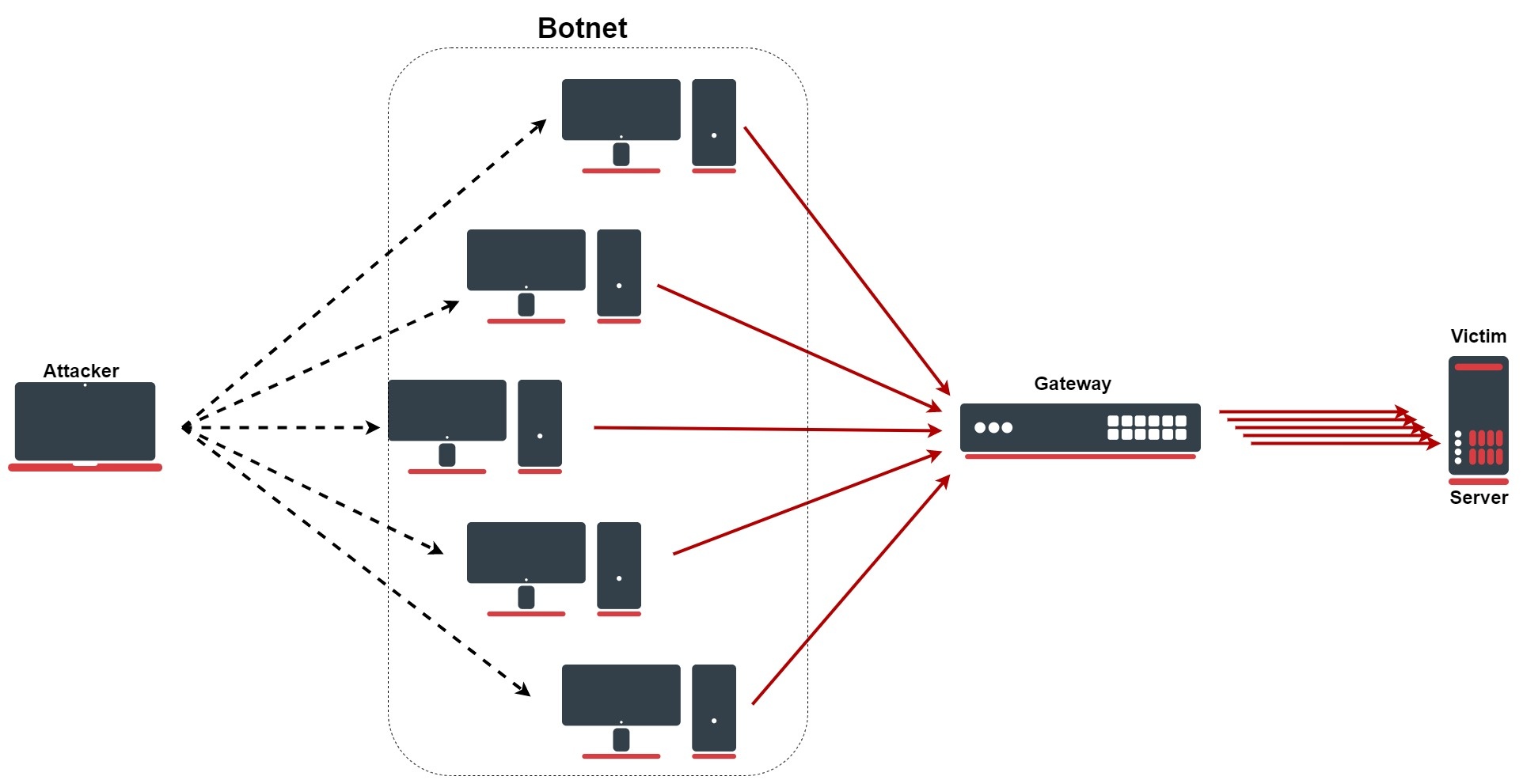
These attacks mainly aim to overwhelm a hardware or its surrounding infrastructure by sending an unusually large traffic volume, referred to as a flood, and force the device either to crash or to stop legimitizing the incoming traffic. The result will be a disrupted network or hardware that will eventually lead to an attacker gain unauthorized access to various network sectors.
Yes, it sounds threatening, and yes, it can be a major headache. That is exactly why we recommend you spend a little more than 10 minutes to learn how easily and effectively you can contain and stop DDoS attack in RouterOS.
Why Does it Matter?
Let's answer this question with an example.
In 2010, back when PayPal was still owned by the marketplac giant eBay, an enormous DDoS attack occured in the U.S. after PayPal suspended its services to WikiLeaks. This attack, conducted by the hactivist collective Anonymous, targeted PayPal, as well as MasterCard and Visa and some other notable organizations.

More than a hundred eBay employees worked for three weeks to recover from this cyber campaign - titled Operation Paycheck - and resume services. Moreover, the company had to spend an ungodly amount of money to bolster its network infrastructure, which, at that time, was already noteworthy in terms of its security.
In short and according to the BBC, PayPal suffered £3.5m as a result of this DDoS attack.
A Bit of Care Goes a Long Way...
You'd be surprised how easily one can secure an edge device to make sure the network behind it is safe and smoothly running.
Some of the most basic firewall configurations, like creating a rule with the Drop action as we discuss in the video above, can reliably fend off a great variety of cyber threats. Therefore, for your sanity and the sake of your business and clients, we highly recommend you watch Session 37 of our Online MTCNA Program and save yourself a great deal of hardship, time and money.
All the MikroTik Knoweldge You Need!
Our online MTCNA course is always freely available on YouTube and you can visit our channel on YouTube as more episodes are posted.
Nevertheless, many of you might have already acquired your MTCNA certificate and are looking for advanced MikroTik engineering courses. Well, good news! We're accepting registrations for a number of online or in-person courses! Drop by our Training webpage down below to find the list of all available classes and their schedule!
MikroTik News
Join the first-ever free MikroTik MTCNA training in Canada! Watch the full course online, get certified, and kickstart your networking career—100% free.
Join the first-ever free MikroTik MTCNA training in Canada! Watch the full course online, get certified, and kickstart your networking career—100% free.